Fraudsters have many ways to steal your identity and money, but there are simple steps you can take to protect yourself.
Given how much valuable personal data we store online, scammers have a strong incentive to try to steal it. With just a few personal details, they can steal your identity, clean out your bank account, run up credit card bills, or commit crimes in your name.
In 2022, the Federal Trade Commission (FTC) received over 1.1 million reports of identity theft(new window) in the US. And for those affected, the impact can be devastating.
Over 30% of identity theft victims last year said they lost more than $10,000, according to the Identity Theft Resource Center(new window). Most also reported suffering negative feelings and emotions or even physical problems as a result.
But there are ways to protect yourself. We explain how scammers can steal your identity and what you can do to stop them.
How fraudsters steal your identity
How to spot phishing and social engineering
What to do if you suspect phishing
10 ways to prevent identity theft
1. Don’t respond to spam!
2. Get secure email
3. Hide your email with aliases
4. Use strong passwords and 2FA
5. Install good anti-virus software
6. Keep your devices updated
7. Back up your data
8. Use a trustworthy VPN
9. Don’t overshare personal data
10. Protect your physical documents
Stay secure with Proton
How fraudsters steal your identity
Fraudsters steal personally identifiable information, like your name and address, credit card or bank account numbers, or Social Security numbers. They can then buy things with your credit card, access your bank account, steal your tax refund, and more, while you pick up the tab. Or they may use your identity to commit other crimes, pretending to be you.
Here’s how thieves can get your personal details to steal your identity:
Phishing and social engineering
Phishing is an online scam in which attackers send you fake emails or text messages to trick you into revealing sensitive information or downloading malware on your device. Or they may call you asking for personal details or use other social engineering(new window) tricks to defraud you. See how to spot phishing below.
Hacking and data breaches
Malicious hackers can target organizations that store large amounts of personal data, like banks, email providers, or online retailers. Once your personal details are leaked in a data breach, they can be sold on the dark web.
Malware
Malware(new window), such as spyware or Trojans, can be downloaded onto your device by phishing emails, software installations, or other means. Fraudsters may use it to steal personal details like login credentials or even take control of your device.
Social media
Scammers can learn a lot about you just from what you post online, so be careful what you share. They can also set up fake social media profiles and ask to connect to gain access to your private posts.
Skimming
Criminals can install skimming devices on ATMs, fuel pumps, or other payment terminals to capture your credit card details. When you insert and use your card, they steal your card number and PIN.
Your trash
If you discard or recycle sensitive documents like bank statements or utility bills without shredding them, beware. Fraudsters can raid your trash to salvage your personal data.
Physical document theft
Thieves can also steal personal data from documents you leave lying around, so keep your documents secure. Similarly, they can target your mailbox outside your home, so keep it locked.
Government records
If you live in the US, personal data like criminal records, property owner information, and other public records are freely available. Anyone can legally gather this information on you and sell it to others, including scammers.
From you
You may give away reams of personal data if you participate in surveys and competitions or fill out product warranty cards on paper or online. All this data can be sold to others legally or as part of a scam.

How to spot phishing and social engineering
Phishing is one of the most common ways fraudsters attack online. In 2022, the FBI received around 800,000 complaints of internet crime in the US, and over 300,000 were related to phishing(new window).
That’s why it’s essential to learn how to spot phishing attempts. Typically, phishing messages contain urgent requests, threats, or promises of prizes, asking you to take immediate action.
Scammers may:
- Say they’ve noticed “suspicious” login attempts on one of your online accounts and ask you to “confirm” your login details
- Claim you need to “verify” your personal or financial details, like your credit card number, or your account will be closed
- Say you’ve been selected for a “special offer, a “lottery win”, or you’re due an unexpected “tax refund” and then request your bank account details to “pay” you
- Send you a connection request on a social media network or dating site, but you don’t know the person and aren’t registered with that site
Besides this dubious content, phishing emails may contain other fraudulent signs, such as fake sender addresses, generic greetings, or suspicious links or attachments. Learn how to spot a phishing email.
What to do if you suspect phishing
While the content and format of many phishing emails give them away as “phishy”, some appear to be from genuine senders, so beware!
We recommend taking the following steps when you receive any email with a button, link, attachment, or request for personal details, especially if it appears urgent:

If you’re unsure about a message that appears to be from your bank, for example, contact the bank directly or log in to your account to check. Only don’t use the contact details or login links in the message.
10 ways to protect yourself against identity theft
Being aware of phishing is just one way to protect yourself. Here’s how to ensure you don’t become an identity theft statistic:
1. Don’t respond to spam!
Don’t open or respond to spam or suspicious (phishy!) emails. Above all, don’t click on links or attachments or reply to requests for personal details. Delete.
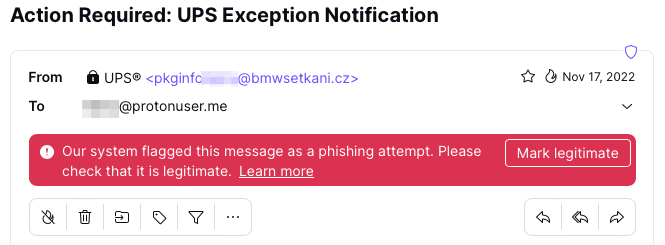
2. Get secure email
Get end-to-end encrypted email, like Proton Mail, with smart spam filtering and PhishGuard advanced phishing protection. PhishGuard sorts and flags suspicious emails in your inbox, alerting you to phishing attempts.
3. Hide your email with aliases
Use email aliases to keep your personal email address private. A good email aliasing service, like SimpleLogin by Proton(new window), allows you to create a unique email address for different services. That way, you can easily trace the source of spam or phishing emails and revoke the alias if it’s being abused.
4. Use strong passwords and 2FA
Create strong passwords and get a good, open-source password manager, like Proton Pass, to secure your accounts. And switch on two-factor authentication (2FA) wherever you can. With 2FA, if your login credentials are ever leaked, fraudsters won’t be able to access your accounts.
5. Install good anti-virus software
Install reputable antivirus software, which can scan your computer or phone for malware used to steal your data. Antivirus software can also give you real-time protection, monitoring emails, attachments, and web content to flag potential phishing emails or software vulnerabilities.
6. Keep your devices updated
Make sure your computer and phone operating systems and other apps are updated to the latest versions with security patches. This will protect you against malware that exploits software vulnerabilities.
7. Back up your data
Make regular backups of your data, including offline backups using an encrypted external drive. While this won’t prevent identity theft, it will help you restore your data from a clean backup if your device is ever infected with ransomware or spyware(new window).
8. Use a trustworthy VPN
Get a trusted virtual private network (VPN)(new window) like Proton VPN(new window). A VPN encrypts your internet traffic, protecting any sensitive information you share over insecure networks like public WiFi. VPNs also hide your IP address and location, making it more difficult for cybercriminals to trace you online.
9. Don’t overshare personal data
Be careful what you post on social media. Don’t reveal sensitive details such as your date of birth and home address. And avoid revealing reams of personal data in surveys, competitions, product warranty cards, or other forms.
10. Protect your physical documents
If your mailbox is outside your home, lock it. That will prevent criminals from stealing your mail containing sensitive information.
Stay secure with Proton
Identity thieves have many ways to steal your personal data, but the steps above should keep them at bay.
But no matter how careful we are, we all make mistakes. Even seasoned IT professionals can fall for a phishing email or find their data exposed in a data breach.
At Proton, our mission is to give everyone privacy and security online. We’ve designed Proton Mail to give you the best chance against phishing and identity theft, including:
- End-to-end and zero-access encryption to protect your information in a data breach
- PhishGuard advanced phishing protection to alert you to potential phishing emails
- Smart spam detection and custom filters to automatically filter spam
- Link confirmation to let you check the URL in links before you open them
- 2FA with authenticator apps and security keys to secure your account
- Address verification to confirm that senders in end-to-end encrypted emails are genuine
- Aliases to hide your personal address from spammers and scammers
- Our Official badge to make it easy for you to identify which emails came from Proton
All Proton plans include end-to-end encrypted Proton Mail, Proton Calendar, Proton Drive, and Proton VPN(new window) to secure your internet connection wherever you are. So get Proton Mail free, and stay secure!






